Cyber risk is now a major issue for businesses as Australia undergoes a rapid shift in data and cyber security regulation, with new laws emerging on cyber, critical infrastructure, privacy, and AI. On 30 October in Sydney, our TMT Summit brought together experts to explore how organisations can build resilience and respond to cyber incidents amid these changes.
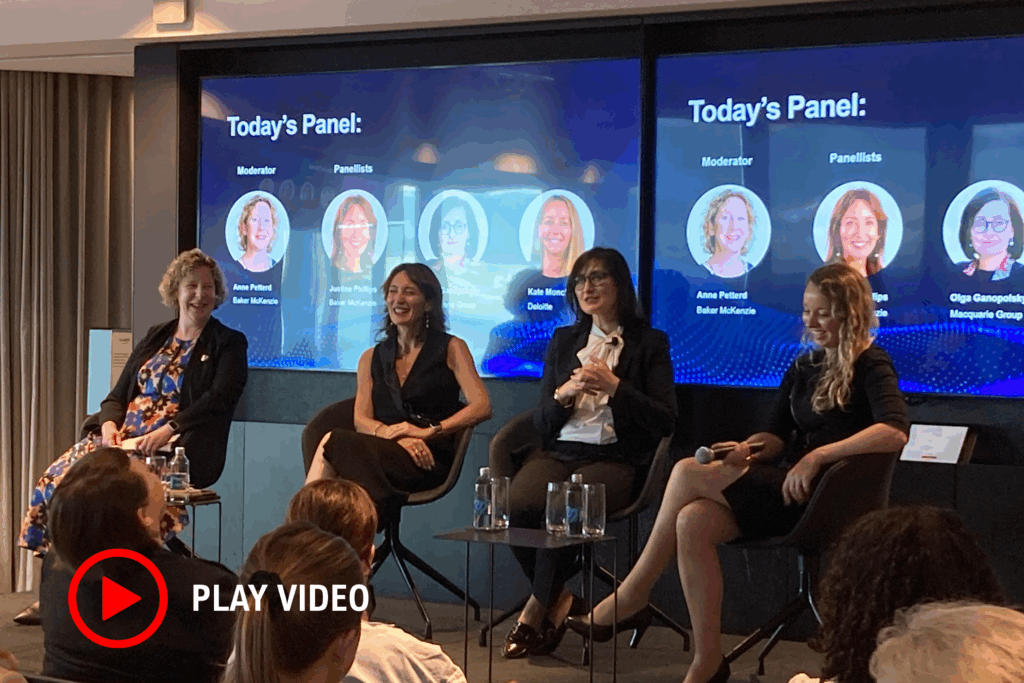
The Panel was moderated by Anne Petterd (Partner – Baker McKenzie, Sydney) and panellists included Olga Ganopolsky (General Counsel, Privacy and Data – Macquarie Group), Kate Monckton (National Lead Partner, Enterprise Security Practice – Deloitte) and Justine Phillips (Partner & Co-Chair North American Data & Cyber Practice Group – Baker McKenzie, Los Angeles).
The expert panellists discussed the rapid transformation of the cyber security landscape as it navigates the uncertainty of new (often AI-advanced) threat actors and an evolving geopolitical landscape, highlighting the importance of protecting critical infrastructure and addressing supply chain vulnerability. Panellists and guests brought together legal, governance and strategic perspectives on how best to navigate this uncertainty and increasing regulatory scrutiny, and shared insights on how individuals and organisations can prepare for this type of incident. This included:
- The importance of fostering a culture of information sharing within the tech space to strengthen collective cyber resilience. Shared knowledge enables faster identification and mitigation of emerging threats. By openly exchanging threat intelligence organisations can stay ahead of adversaries and build a more secure digital ecosystem together.
- Getting “match-fit” for incident response. Education and training across all seniority levels and disciplines within an organisation is essential to guarantee informed decision-making and a harmonised response during a cyber incident. Ensuring that the organisation has fall backs (an A, B and C team ready to step up if certain representatives are unavailable), who are all well-educated and ready to respond.
- The complexity of cybersecurity requires multidisciplinary planning, with each workstream performing their respective roles. Establishing solid processes is key to adequately empowering your CISO. As organisations are on alert following the penalties issued in the Australian Clinical Labs decision, keep lawyers in the room when you place cyber in front of key decision makers.
Click the image below to watch the highlights reel